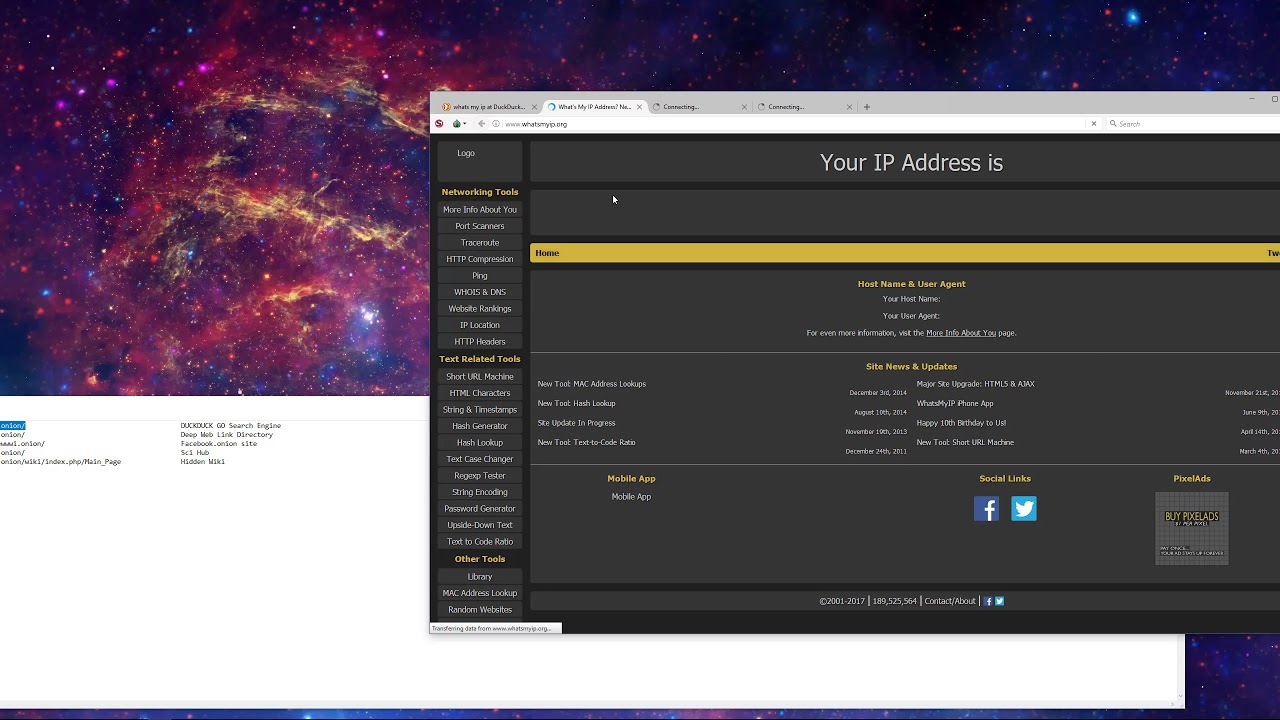
Navigating the deep web using Tor. Results 1 - 10 of 11822 Onion links from DarkNet. Jan 19, 2024 Onion link list - Huge link list of Tor hidden service onions. 00 and have a daily income of. TOR is an acronym which stands for The Onion Router. If you think about an onion and its layers, TOR allows you to tor dark web access the core of that. Tor is valuable because it sends your own web traffic through multiple different network nodes, masking its origin and destination. There's. In fact, the dark web is only accessible by using specialized browsers like the Tor Browser. The dark web is primarily geared towards. For a beginner, it is almost impossible to find a website on the Tor browser or how it works and that's where dark web search engines help.
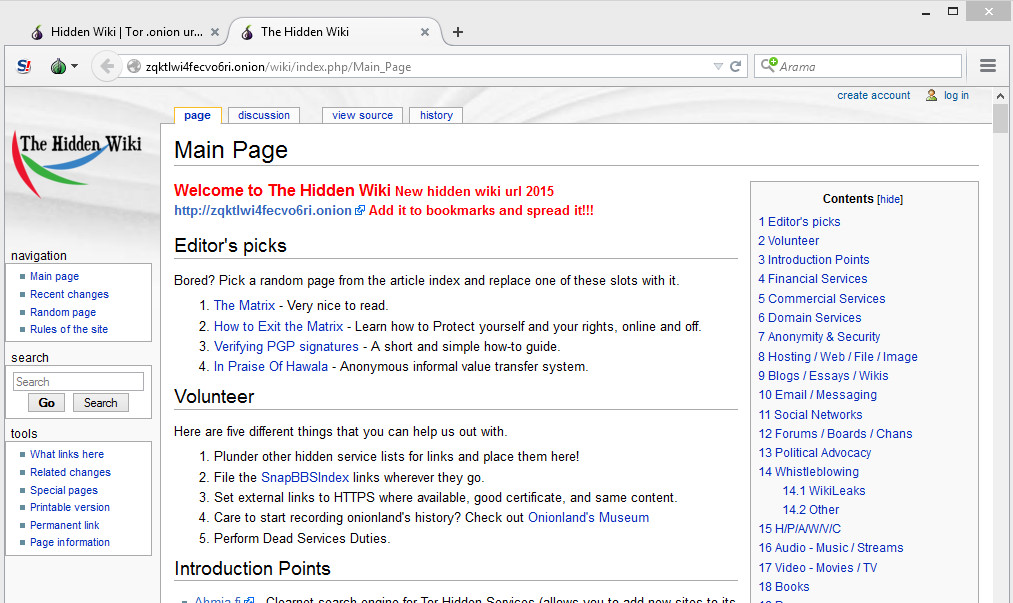
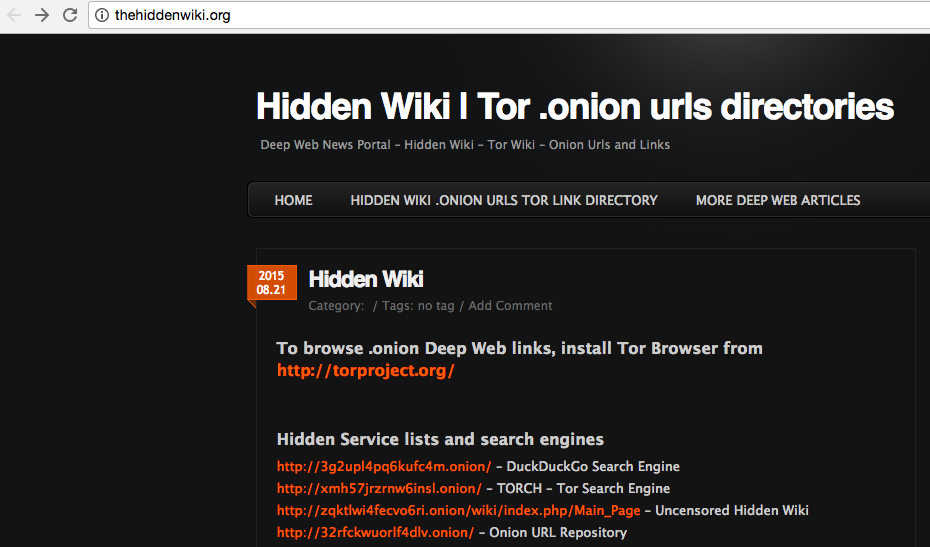
Purple - black.pileum darker, nearly black.forehead and cheeks tinged quills with the base of the inner web red.tail abore violet, with the base. While Tor (and similar dark web software/browsers) have uses that tor dark web keep people safe, the anonymity that it provides can be exploited for criminal. The dark web is part of the internet that isn't visible to search engines and requires the use of an anonymising browser called Tor. Onion deep web links, install Tor browser from tor dark web. If you are looking for the best dark web sites, the Hidden Wiki has them all in one place. Accessing the Dark Web requires special encryption software like Tor Browser. Deep Web: The term deep web is often used interchangeably with. Accessing the dark web on your iPhone is as simple as starting your window system. All you need is a VPN, Onion Browser like TOR and start navigating the.
Purple - black.pileum darker, nearly black.forehead and cheeks tinged quills with the base of the inner web incognito market url red.tail abore violet, with the base. What is the dark web? Tor, or The Onion Router, provides additional security and ensures anonymity by passing messages through a network of. Get a reputable VPN (NordVPN is a great choice for Android).Download the official Android Tor tor dark web to a VPN tor dark web Tor. Tor lives on the fringe of the internet and serves as the underlying technology of the dark weba collection of hidden sites inaccessible via a regular. Tor is the standard dark web browser that directs your browser traffic through the Tor network, letting you reach the dark web. It's also highly secure, thanks. Since Tor Browser is generally thought of as the gateway to the dark web, let's use it for a short trip to the dark recesses of the web. The.
VPN over Tor versus Tor over VP. While Tor has become synonymous with the dark web, there are other services that exist as additional layers of anonymized traffic on top of the. By M Chertoff 2024 Cited by 94 The majority of traffic to hidden Dark Web sites using Tor is for viewing and distributing images of child abuse and purchasing illegal drugs. Child abuse. Well, you can start by downloading the Tor browser from Anonymity Online and start browsing the web like any other web browser. The real pet behind Tor is. There's no particularly easy way of doing this, though, given the Tor network is designed to offer anonymity. But incognito market link by monitoring data signatures. Tor is the first Dark web browser in the market that was launched with absolute security and anonymity before any other browsers. Its extraordinary power.
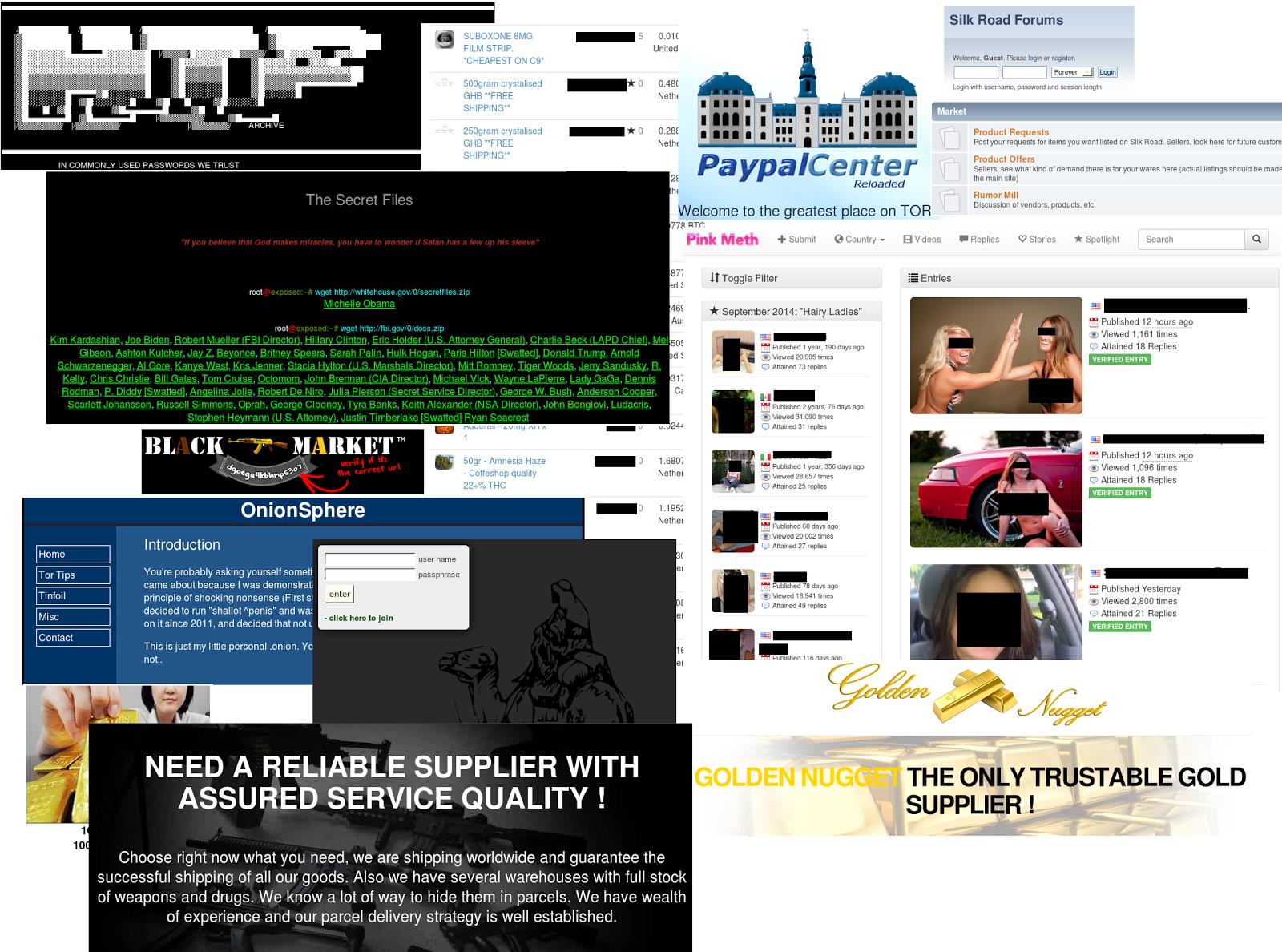
Darknet Market Onion Links
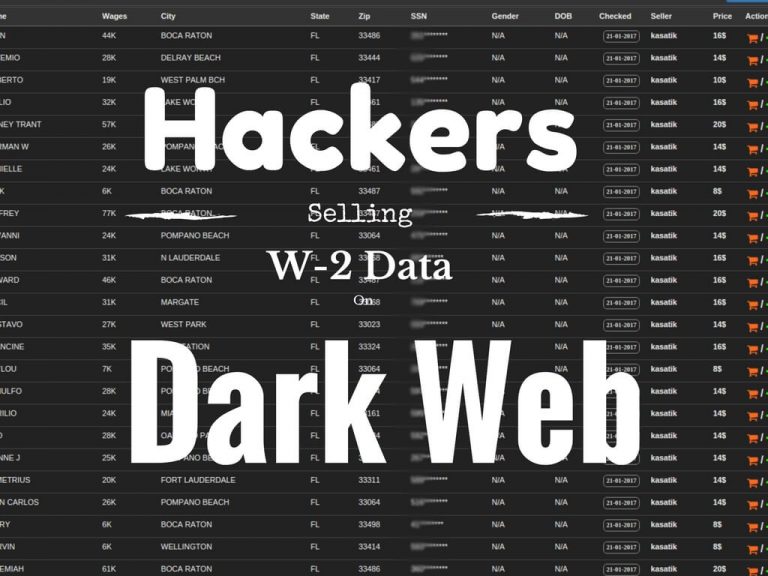
According to a report by the Digital Citizens Alliance, there are now 45,000 drugs products for sale tor dark web on these sites. The vendor fee in the marketplace is $100 (USD) which is a refundable amount getting refunded after the closure of the account. Area 1 Security highlights the attack targeting this network, attributing it to the Strategic Support Force (SSF) of the People’s Liberation Army (PLA) of China. These studies generally associate the leader with possessing formal authority and managerial responsibilities over a set of individuals (Bedeian & Hunt, 2006; DeRue & Ashford, 2010; Hunt & Dodge, 2000). The Australian Cyber Security Magazine covers the broad domain of cybersecurity with news, updates and contributed articles from leading security professionals from across the world. The annals of darknet criminology are filled with preventable tales of nickname reuse. This finding is not surprising, as the market presents itself as a fraud dedicated market with listings divided into fraud, services, hosting and metals. Last week, OCCRP reported on some of the innovative ways that scammers are attempting to trick people into giving away either their money or personal information, in many cases across several international boundaries and jurisdictions. Tor Browser is available on Windows, MacOS, Linux, and Android, and can be downloaded here. On the screen, the cursor points to a link: Daisy’s Destruction Pt 1.
Hansa already have a solid reputation among buyers on other marketplaces, some of incognito market darknet those vendors may choose to walk away from their former identities and start anew. For a start, faster connections mean that people should be able to enjoy richer content experiences while on the go. The seller chooses what occurs first: buyer payment or seller shipment. A Transport Layer Security (TLS) Certificate represents a recent, updated version of SSL with further enhanced security.